 No. Hackers who are caught may face legal penalties and fines. Blue Hat Hackers are vindictive script kiddies who hack as a approach of exacting revenge against their enemies. “The word hack doesn't really have 69 different meanings”, based on MIT hacker Phil Agre. Youll have that paper in your boss or professors desk in time – even if you happen to run out of ink. As technology progressed, however, opportunities for financial gain by illegal activity, burgeoned, from which arose criminal hacking enterprises which are run similar to another business. 799 USD excluding the computer that is required to run it. Originally, a hacker was defined as one who is enthusiastic about computers, whether that be programming or entering into the guts of a computer to see how it works. Most of us are used to see the My Computer page instead. As a result of their curiosity, they are self-motivated and spend hours learning, practising and improving upon their skills. In the beginning, most hackers were motivated by curiosity, learning and challenges.
No. Hackers who are caught may face legal penalties and fines. Blue Hat Hackers are vindictive script kiddies who hack as a approach of exacting revenge against their enemies. “The word hack doesn't really have 69 different meanings”, based on MIT hacker Phil Agre. Youll have that paper in your boss or professors desk in time – even if you happen to run out of ink. As technology progressed, however, opportunities for financial gain by illegal activity, burgeoned, from which arose criminal hacking enterprises which are run similar to another business. 799 USD excluding the computer that is required to run it. Originally, a hacker was defined as one who is enthusiastic about computers, whether that be programming or entering into the guts of a computer to see how it works. Most of us are used to see the My Computer page instead. As a result of their curiosity, they are self-motivated and spend hours learning, practising and improving upon their skills. In the beginning, most hackers were motivated by curiosity, learning and challenges.Then glue or tape fabric, pretty wrapping paper or wallpaper to the poster board. You may lower a piece of plywood to size, cover with wallpaper or sand and paint, add to the back. Navigate back to your house folder before continuing. For dwelling users and dwelling bussiness partners faceing that problems is usually more devistating. Check our inclusion policy for more information. Turn Windows feature on or off and examine the option for Telnet Client. With Windows 7's "shake" feature, though, you may minimize every window except the one by which you're at present working -- in a single step. Issues like low self-esteem, poor impulse control and anger management problems can exacerbate the descent into the world of predatory hacking. 1 - Script Kiddies & Other Novices - Script kiddies, referred to as skids for short, have a low skill set and typically use code, written by others. Script kiddies and white, black and gray hats can all be found in a hacktivist collective, comparable to Anonymous. As an example, when a gray hat hacker hacks a website, they might tell the site owner about the vulnerability that allowed the hack to take place. Hence, a hacker may hack for malicious or favorable purposes, but even a effectively-intentioned hacker could be led astray.
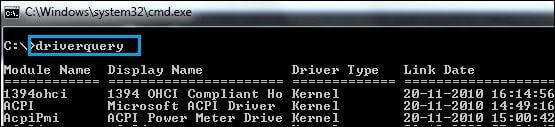
You may play this game using your iPhones, Android gadgets, and even on your Facebook. You can even use the ping command to find the IP deal with. Which connotation is implied by a given use of the word depends in similarly profound ways on the context. Script kiddies tend to lack motivation and rarely perform their own hacks, preferring to utilize easy to use software. Green Hat Hackers are also newbie hackers, but unlike script kiddies green hats have the drive to change into more advanced hackers. It is a virtual iPhone memory hack that tricks the iPhone into thinking it has more memory than it physically does. The IHTFP Hack Gallery staff does not encourage trespassing, or another illicit activity. Why isn't my favorite hack in the IHTFP Hack Gallery? “In fact, hack has only one meaning, an extremely subtle and profound one which defies articulation. Find the spectator's match without looking -- in only one second!
Engaging in humorous and sometimes challenging pranks seems to be one such outlet. If you are using a Mac, you may be on your own. Who are the hackers? Currently, there is a significant shortage of hackers or cybersecurity professionals who are employed by businesseses and governments, including militaries. Leaking information, doxing, reporting terrorist accounts on social media and raising awareness of issues deemed essential are also measures taken by hacktivists. This may increasingly involve DDoSing the websites of organizations accused of cruelty to animals, terrorist websites, the websites of oppressive government regimes, and many others. It also can involve hacking the websites of governments with whom the hacktivists disagree, in regard to policy. A script kiddie will usually not progress beyond doxing and performing simple DDoS attacks on websites. You will be successful in choosing professional outsourced IT services if you take help of the Internet. If you already know how many coins each crop type gives you, it will assist you to know what to plant, for how long and how much money you'll make.
Comments
Post a Comment